Audit logging for knowledge base compliance
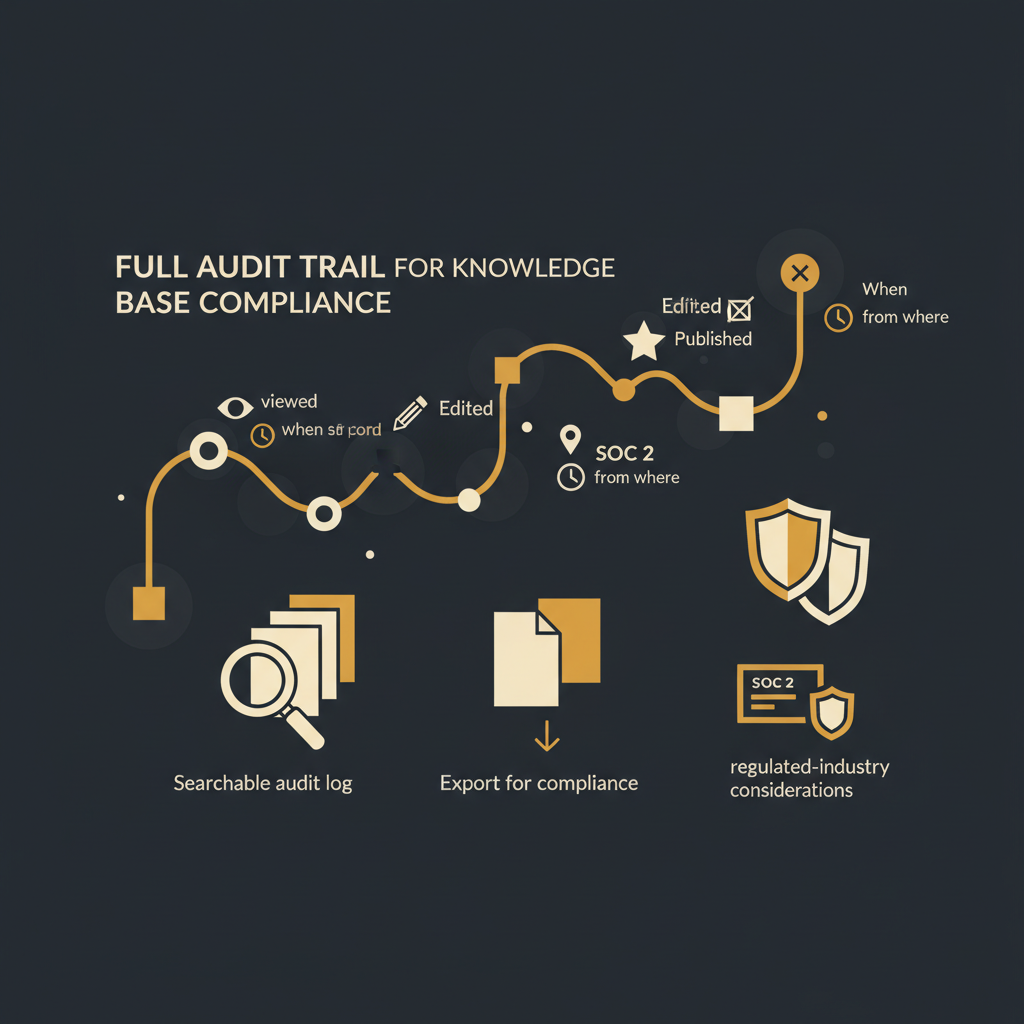
Maintaining a compliant knowledge base requires more than just good content; it demands a verifiable record of every interaction. Understanding who viewed, edited, published, or deleted what, when, and from where is crucial for operational integrity and regulatory adherence.
In an era where every operational process is rigorously scrutinized for compliance, security, and efficiency, the knowledge base has fundamentally transformed. No longer a static repository of documents, it is a dynamic, mission-critical system, central to customer support, engineering operations, and sales enablement. It houses definitive answers, standard operating procedures, and critical guidance. Without a clear, immutable record of activity, this vital resource poses significant risk. For senior leaders in operations, customer success, and engineering, the modern knowledge base is not merely about content consumption; it is fundamentally about accountability and verifiable operations, particularly in highly regulated industries where meticulous documentation and unimpeachable evidence are paramount to maintaining operational integrity.
The Imperative for Granular Knowledge Base Visibility
A knowledge base is a living entity, continuously updated, refined, and sometimes, misused. For leaders responsible for organizational process integrity, this dynamism presents unique challenges. Consider when an outdated compliance procedure leads to a regulatory breach, or a critical customer support article is inadvertently deleted. Without a robust, granular audit trail, identifying the sequence of events, pinpointing responsibility, and demonstrating due diligence becomes impossible. This extends beyond troubleshooting; it establishes trust and maintains control over critical organizational knowledge. A comprehensive audit log moves beyond simple version history, providing a meticulously timestamped, user-attributed account of every significant interaction. This ensures the integrity and accuracy of the knowledge base can always be verified, a non-negotiable requirement in today's demanding operational landscape.
Anatomy of a Comprehensive Audit Log: What to Track
An effective knowledge base audit log is a deep, forensic tool, providing an irrefutable chain of custody for every piece of information. The "who, what, when, and where" must be unequivocally answered for each entry.
- Content Lifecycle Events: Every action related to content demands logging: creation, every edit (including drafts), and major updates. The log should capture not just modification, but ideally, a detailed 'diff' of changes made, linking to the user ID, exact UTC timestamp, and article's unique identifier. For example: 'User A modified Article ID 12345 (Title: Onboarding Process) at 2023-10-27T10:30:00Z, changing step 3 from X to Y'. This detail is critical for accountability.
- Publication and Version Control: The moment an article transitions from draft to public (published) or is removed (unpublished) is pivotal. This action must be logged with the initiating user, exact time, and specific version. For regulated content, this timestamp proves when a specific, approved version was active or superseded.
- Deletion and Restoration Operations: Permanent removal or restoration from archive carries significant implications. An audit log must record who deleted what, when, and if applicable, who initiated restoration. This prevents unauthorized information loss, supports data retention policies, and offers a crucial recovery path.
- Access and Viewing Patterns: Logging who viewed which articles, and when, is important for compliance and investigations. For sensitive information (e.g., internal security protocols), this establishes an access record, demonstrating who had sight of specific data, vital for regulations like GDPR or HIPAA.
- Administrative and Configuration Changes: Any alteration to user roles, access permissions, or system-wide settings constitutes a high-priority audit event. This ensures administrative actions are transparent and accountable, preventing unauthorized privilege escalation or data exposure. Example: 'Admin User B changed User C's role from Author to Editor at 2023-11-01T09:00:00Z'.
- Export and Data Egress Activity: If content can be exported, downloaded, or integrated, recording these actions provides an additional layer of data egress control and auditability. This is particularly relevant for intellectual property or sensitive operational data. A log entry like 'User D exported Article ID 67890 to PDF at 2023-11-02T14:15:00Z' provides crucial visibility.
Satisfying Regulatory Compliance and Audit Requirements
For organizations operating under stringent regulatory frameworks, a comprehensive audit log is not merely a desirable feature; it is a fundamental compliance requirement. The ability to produce verifiable, timestamped records of activity is often the cornerstone of demonstrating adherence to various standards and avoiding significant penalties.
Consider the demands of SOC 2 Type 2, where data integrity, system availability, and security controls are rigorously tested. An audit log provides direct, irrefutable evidence for controls such as 'changes to system configuration are authorized, logged, and reviewed' or 'access to sensitive data is monitored.' During an audit, practitioners routinely request specific log entries to validate these controls, looking for clear, unambiguous 'who, what, when, and where' details. The absence of such detailed logs can lead to significant findings and control deficiencies.
Similarly, for healthcare organizations navigating HIPAA, tracking access to any patient-related information or protocols within a knowledge base is paramount. If an article outlines procedures for handling Protected Health Information (PHI), the audit log demonstrates exactly who accessed that protocol, at what time, and from where, thereby validating compliance with strict access control and privacy policies. Without this, proving compliance becomes a subjective and precarious exercise.
In the heavily regulated financial services sector, adherence to standards like PCI DSS or the EU's DORA necessitates robust and immutable logging of all system activities, including those within knowledge management platforms that support critical operations. The capability to produce a tamper-proof, searchable log of all content changes, access events, and administrative actions is crucial for demonstrating resilience, accountability, and the integrity of financial operations.
Even for less directly regulated industries, robust internal governance policies often mandate high accountability. An audit log provides the factual basis for internal investigations, incident response post-mortems, and process improvements. It demonstrates an organization's unwavering commitment to verifiable data stewardship. Furthermore, the capability to search these logs efficiently and export them in common, machine-readable formats (e.g., CSV, JSON) drastically reduces the burden during audit cycles, transforming what could be a multi-day, manual data compilation task into a swift, verifiable query, saving hundreds of hours annually and significantly de-risking the audit process.
The operational integrity and strategic value of a modern knowledge base are inextricably linked to its reliability and the trustworthiness of its content. Without a transparent, irrefutable record of every modification, publication, deletion, and access event, the knowledge base ceases to be a reliable source of truth. Instead, it becomes a black box, a potential source of significant compliance risk, and a barrier to operational efficiency. Implementing a system that provides a full, forensic audit trail for all content lifecycle events is not merely a desirable feature for advanced knowledge management; it is an essential safeguard for any organization serious about data governance, regulatory compliance, and maintaining a verifiable source of truth in an increasingly scrutinized operational environment.
Stop writing docs nobody reads.
Record them instead.
Install the extension, walk through the tool you're tired of explaining. Tome Robot does the rest.